Building Smart Detection for a SOC System (Time-Based Threat Detection)
- Maryam Ziaee
- 2 days ago
- 2 min read
Introduction
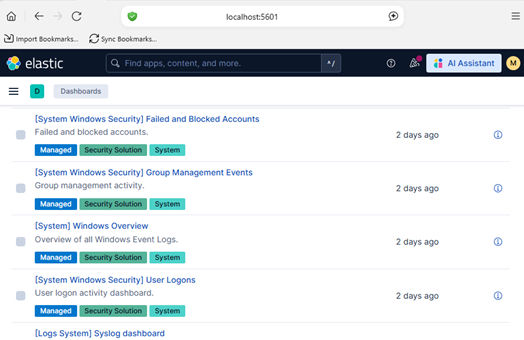
After implementing basic brute-force detection and multi-channel alerting (Telegram + Email), I took the next step toward building a more realistic SOC system: Smart Detection.
Instead of relying on simple thresholds, this phase introduces time-based analysis, making detection more accurate and closer to those found in real-world SIEM systems.
❌ The Problem with Simple Detection
Initially, detection was based on a static rule:
If failed login attempts ≥ 5 → Trigger alert
While simple, this approach has major limitations:
❗ Ignores time context
❗ Generates false positives
❗ Can be bypassed by slow attacks
Smart Detection Approach
To improve accuracy, I implemented time-based detection using ElasticSearch aggregations.
Idea:
Detect multiple failed login attempts within a short time window
Detection Logic
Monitor Windows Security Event ID 4625 (failed login)
Group by username
Analyze activity within 10-second intervals
ElasticSearch Query
aggs: {
users: {
terms: {
field: "winlog.event_data.TargetUserName",
size: 10
},
aggs: {
per_interval: {
date_histogram: {
field: "@timestamp",
fixed_interval: "10s"
}
}
}
}
}
Detection Implementation
for (let user of users) {
for (let bucket of user.per_interval.buckets) {
if (bucket.doc_count >= 3) {
const msg = " SMART DETECTION!\nUser: "
+ user.key +
"\nAttempts in 10s: " + bucket.doc_count;
await sendTelegramAlert(msg);
await sendEmailAlert(msg);
}
}
}
Why This is Better
Compared to basic detection:
Basic Detection | Smart Detection |
Total count | Time-based |
Less accurate | Context-aware |
Easy to bypass | Harder to evade |
Noisy alerts | More meaningful alerts |
Testing
To validate the system:
Generated multiple failed login attempts
Observed activity within short time windows
Result:
Alerts are triggered only during suspicious bursts
Reduced false positives
More realistic detection behavior
Challenges
❗ Understanding nested aggregations in ElasticSearch
❗ Debugging query structures
❗ Handling async alert execution
❗ Tuning thresholds and intervals
Outcome
The system now includes:
Real-time detection
Time-based analysis
Multi-channel alerting (Telegram + Email)
Anti-spam (cooldown mechanism)
Conclusion
By introducing time-based logic, the system moves beyond simple thresholds and begins to resemble a real-world SIEM detection engine.
🚨 From static rules to intelligent detection — building practical SOC capabilities step by step.



Comments