Building a Real-Time SOC Platform from Scratch (Detection → Alerting → Visualization)
- Maryam Ziaee
- 5 hours ago
- 2 min read
I’ve been working on designing a lightweight SOC (Security Operations Center) platform that simulates real-world detection, alerting, and monitoring workflows.
This project is not just a dashboard; it includes a full detection pipeline from log ingestion to incident visualization.
Phase 1 – Detection Engine (Elasticsearch)
I integrated the backend with Elasticsearch (Winlogbeat logs) and implemented detection logic for failed authentication events:
Event ID: 4625 (Windows failed login)
Aggregation using terms on:winlog.event_data.TargetUserName
Brute-force detection logic:
if (user.doc_count >= 5) {
// Trigger alert
}
This allows identifying repeated failed login attempts per user.
Phase 2 – Smart Detection (Time-based Correlation)
To reduce noise and simulate real SIEM correlation, I implemented a time-based detection model using date_histogram:
aggs: {
per_interval: {
date_histogram: {
field: "@timestamp",
fixed_interval: "10s"
}
}
}
Then applied logic:
if (bucket.doc_count >= 3) {
// Smart alert triggered
}
This enables detection of rapid attack bursts (e.g., password spraying or scripted brute force).
Phase 3 – Alerting & Response Layer
Implemented multi-channel alerting:
Telegram Bot API
await axios.post(`https://api.telegram.org/bot${TOKEN}/sendMessage`, {
chat_id: CHAT_ID,
text: message
});
Email Alerts (Nodemailer + Gmail SMTP)
await transporter.sendMail({
from: EMAIL,
to: EMAIL,
subject: 'SOC Alert',
text: message
});
Alert Flood Control (Cooldown Mechanism)
To prevent alert storms:
if (now - lastTime > COOLDOWN) {
// Send alert
}
This ensures alerts are rate-limited per user.
Alert Persistence (Custom Storage)
Instead of relying on external systems, alerts are stored locally:
fs.writeFileSync('alerts.json', JSON.stringify(alerts));
This allows:
Dashboard history
Replay capability
Lightweight persistence
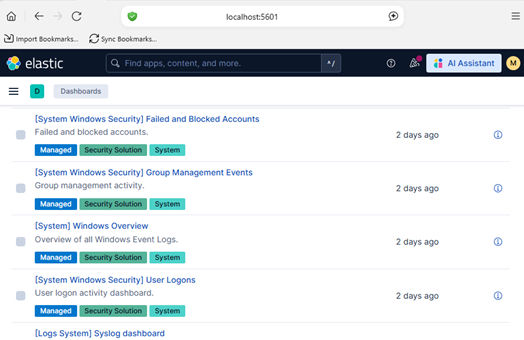
Phase 3 – SOC Dashboard (Frontend)
Built a live dashboard using Chart.js + vanilla JS:
Summary Cards (Active / Critical / High)
Active Cases (simulated case management)
Top Attacker IPs (aggregation)
Attack Timeline (time-series visualization)
Example:
labels: timeline.map(t => t.key_as_string),
data: timeline.map(t => t.doc_count)
Architecture Overview
Logs (Winlogbeat)→ Elasticsearch→ Node.js Detection Engine→ Alerting (Telegram / Email)→ Storage (JSON)→ Frontend Dashboard (Chart.js)
Key Engineering Concepts
Event correlation
Threshold-based detection
Time-window analysis
Alert deduplication
Real-time data visualization
Modular API design
This project is evolving into a mini SOC + SIEM platform, built from scratch.



Comments